Cyber Security & Threat Intelligence Systems
Spade Security delivers fully integrated cybersecurity ecosystems — combining AI-driven threat detection, cloud security management, network monitoring, endpoint protection, and enterprise-grade defense frameworks into one cohesive digital security infrastructure.
From single organizations to multi-site enterprise environments, we design cyber defense systems that detect, analyze, respond, and neutralize threats in real time.
Advanced Cybersecurity Solutions
Enhance operational resilience with Spade Security’s comprehensive cybersecurity systems. Our solutions are built on industry-recognized security frameworks and best practices, delivering secure network protection, real-time threat detection, advanced encryption, and reliable performance to safeguard your critical digital operations.
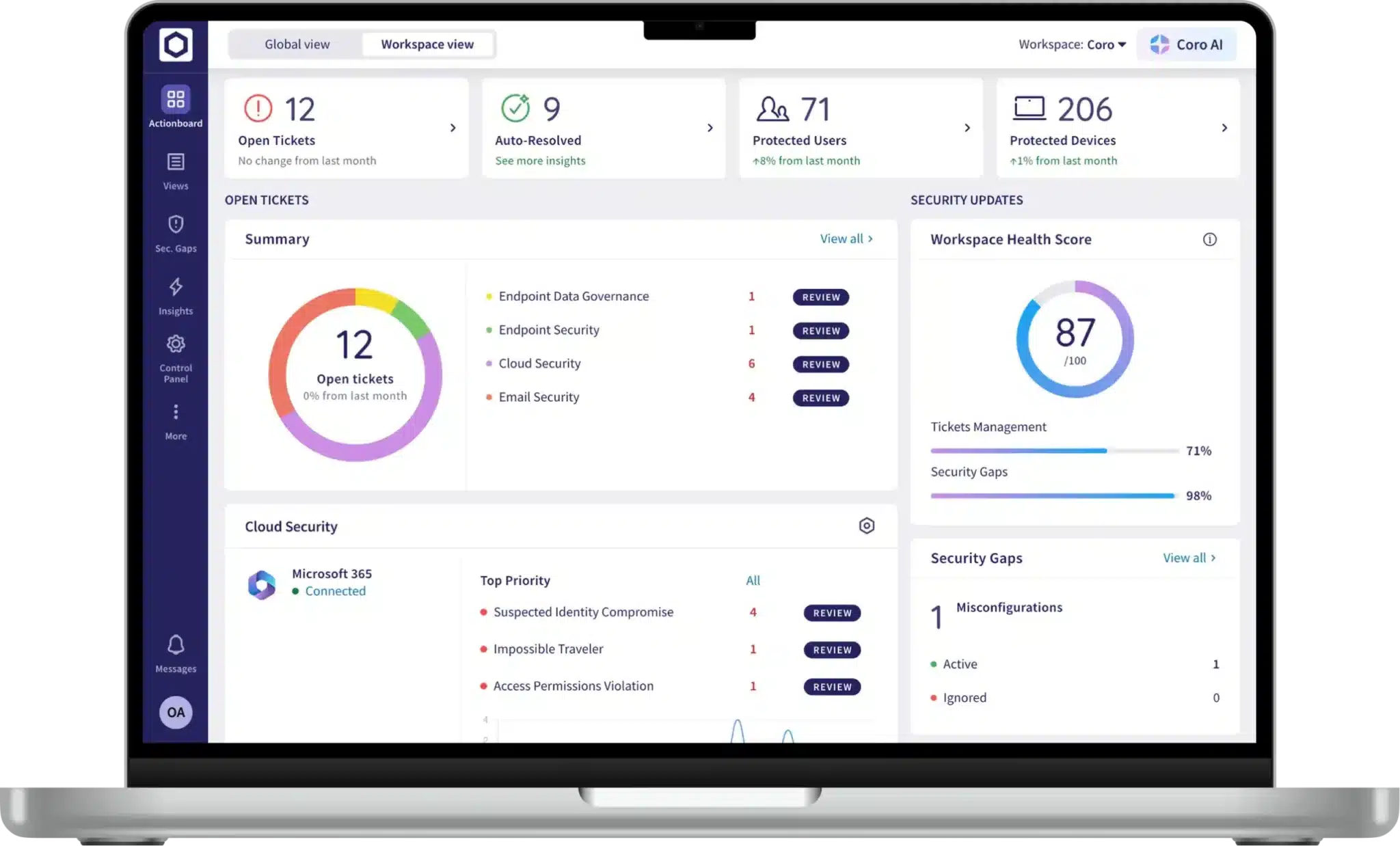
CORO - UNIFIED GUARD SYSTEM
Coro is a unified cybersecurity platform designed to simplify security operations by consolidating multiple protection layers into a single dashboard. It protects email systems, endpoints, cloud applications, and user identities without the complexity of managing separate tools.
Through Spade Security Services, Coro is deployed to reduce operational gaps, automate threat detection, and streamline incident response—giving organizations enterprise-grade protection with minimal administrative overhead.
Specializations / Specifications:
• Email Security (Microsoft 365 & Google Workspace)
• Endpoint Detection & Response (EDR)
• Cloud App Security & Monitoring
• Data Loss Prevention (DLP)
• Ransomware Protection
• Automated Threat Detection & Remediation
• Centralized Security Dashboard
GUARDZ - Managed Cybersecurity for Growing Businesses
Guardz delivers AI-powered, managed cybersecurity tailored for growing businesses that require enterprise-level protection without enterprise-level complexity. It provides continuous monitoring across users, devices, and cloud environments.
Spade Security integrates Guardz to provide proactive defense, identity protection, and automated remediation—ensuring threats are detected and contained before they disrupt operations.
Specializations / Specifications:
• AI-Driven Threat Detection
• Identity & Access Protection
• Endpoint Security Monitoring
• SaaS & Cloud Protection
• Automated Incident Response
• Continuous Risk Assessment
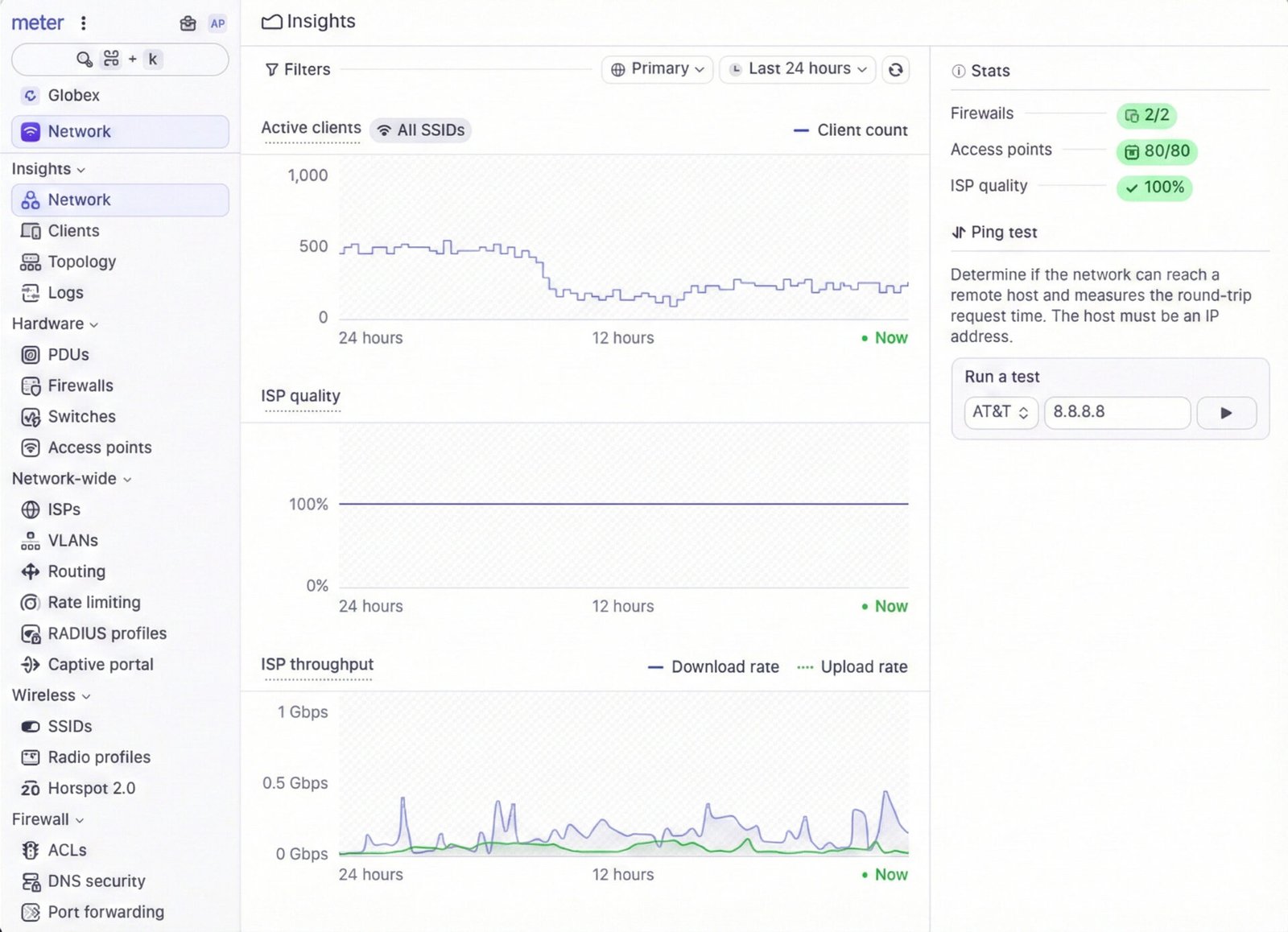
METER - Managed Networking Infrastructure
Meter provides fully managed networking infrastructure that combines internet connectivity, firewall protection, switching, and wireless systems into a single service model. It eliminates the complexity of managing multiple networking vendors.
Spade Security deploys Meter to build secure, scalable, and performance-optimized network environments that support both operational efficiency and cybersecurity defense.
Specializations / Specifications:
• Managed Firewall & Gateway Security
• Secure SD-WAN
• Enterprise Switching Infrastructure
• Wi-Fi 6/6E Access Points
• Network Monitoring & Analytics
• Built-in Redundancy & Failover
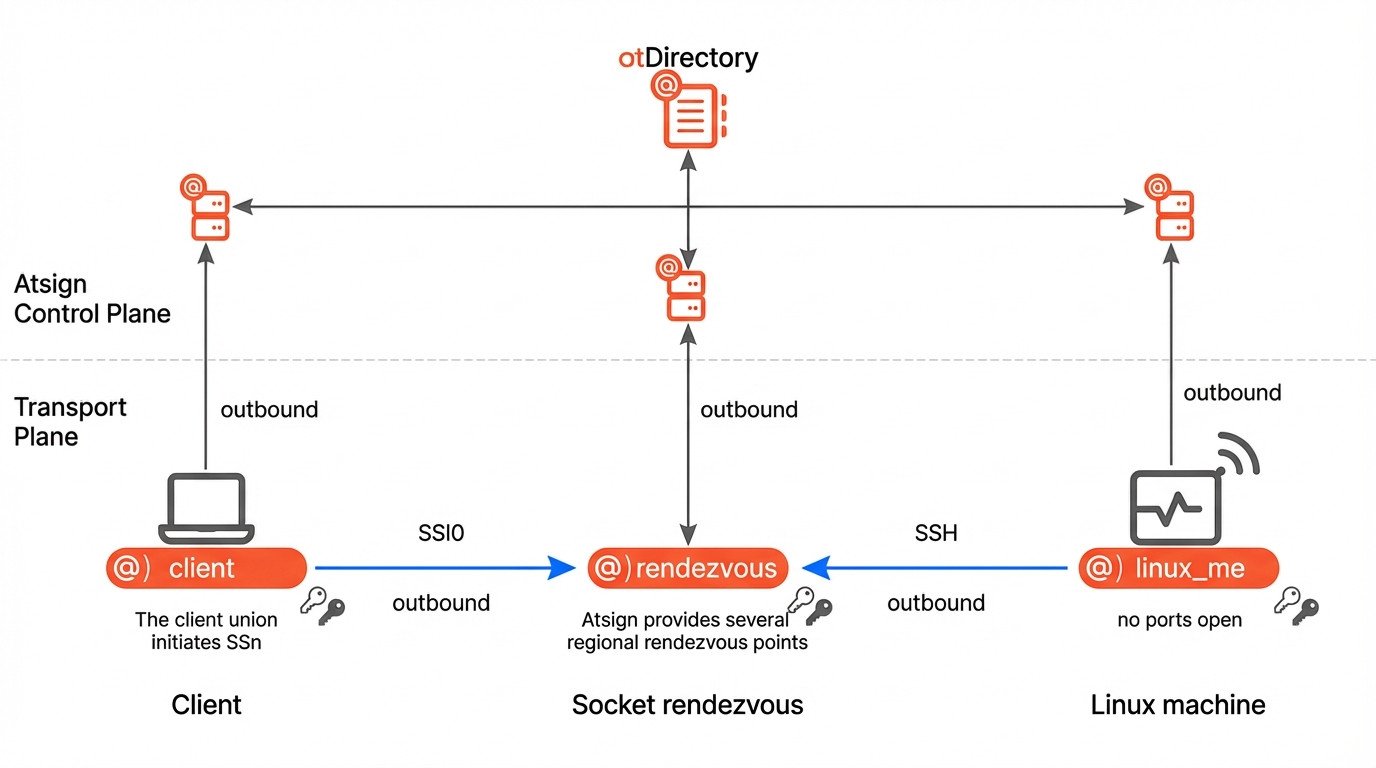
ATSIGN - Secure Communication & Privacy Platform
atSign delivers secure, identity-based communication technology designed to protect sensitive data without exposing IP addresses or relying on traditional centralized servers. It enables encrypted, peer-to-peer data exchange.
Spade Security leverages atSign to strengthen digital identity protection and enable secure communication channels across devices, users, and systems.
Specializations / Specifications:
• End-to-End Encrypted Communication
• Identity-Based Networking
• Zero-Trust Architecture
• Secure Peer-to-Peer Messaging
• Privacy-First Data Exchange
ThreatCop – Security Awareness & Phishing Simulation
ThreatCop enhances organizational cybersecurity by focusing on the human layer of defense. It provides interactive awareness programs and realistic phishing simulations to reduce employee-related vulnerabilities.
Spade Security deploys ThreatCop to build a security-first culture, strengthen compliance posture, and reduce phishing and social engineering risks.
Specializations / Specifications:
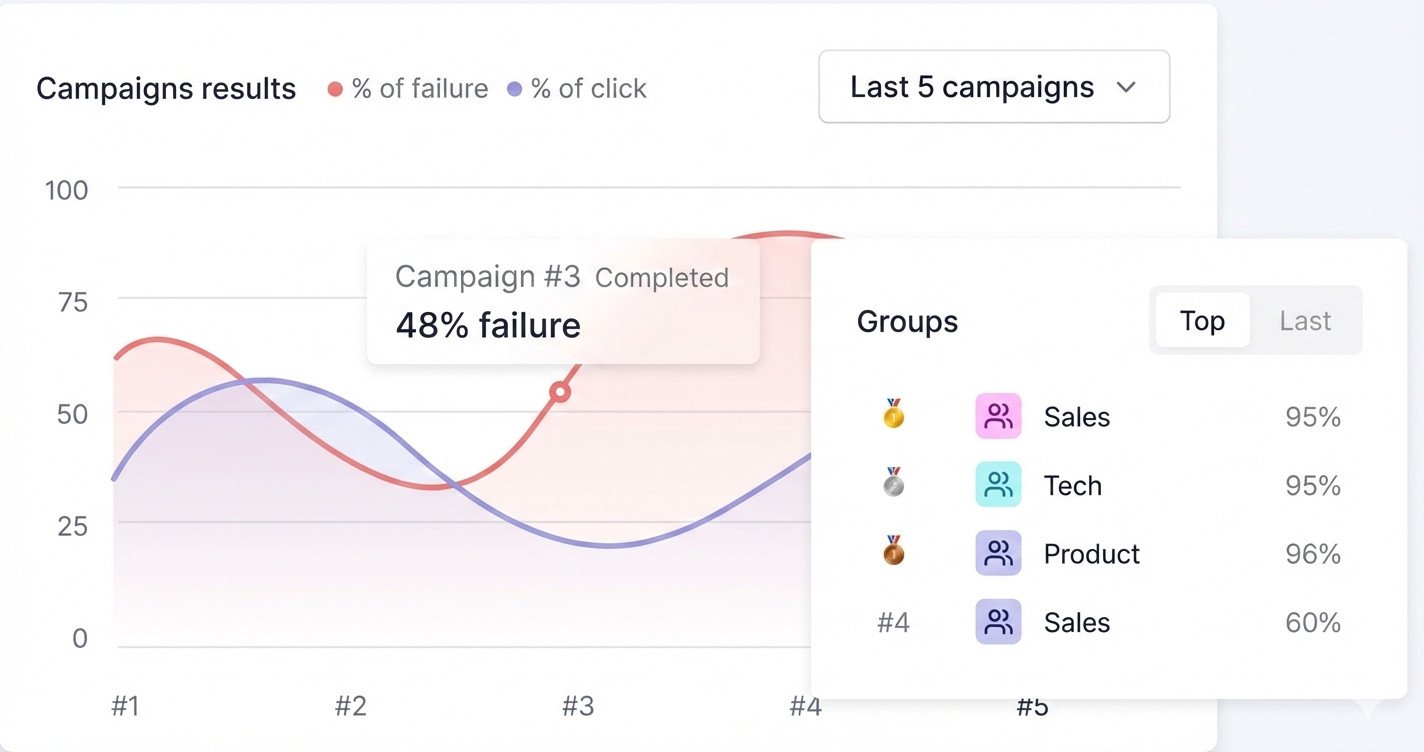
• Phishing Simulation Campaigns
• Security Awareness Training Modules
• Behavior-Based Risk Scoring
• Compliance-Focused Training (ISO, NIST, etc.)
• Reporting & User Risk Analytics
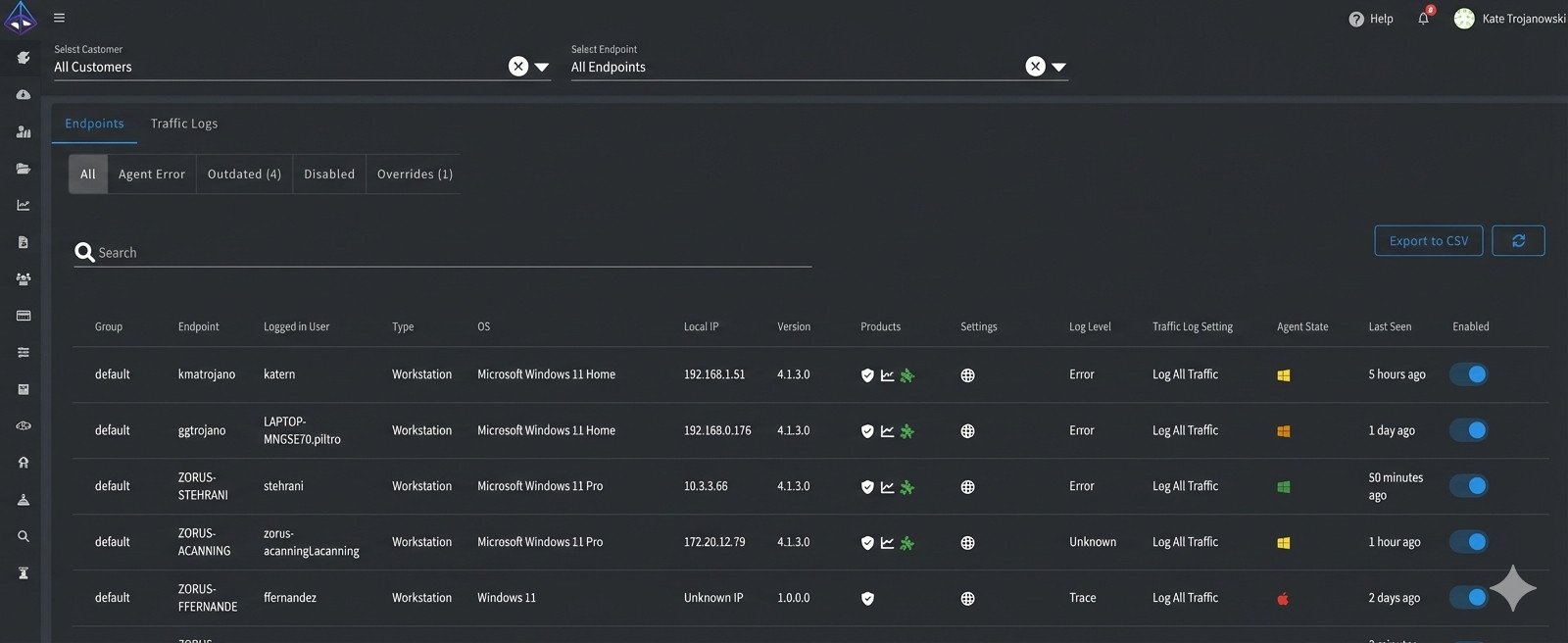
Zorus – Intelligent DNS Filtering & Web Security
Zorus delivers DNS-layer security that blocks malicious domains and harmful web traffic before threats reach the network. It acts as a proactive shield against ransomware callbacks and phishing attempts.
Spade Security integrates Zorus to provide real-time web filtering, content control, and enhanced network visibility across all users and devices.
Specializations / Specifications:
• DNS-Based Threat Filtering
• Ransomware Callback Prevention
• Real-Time Malicious Domain Blocking
• Content Filtering & Policy Control
• Network Traffic Visibility
Elba Security – Human Risk & Security Awareness Platform
Elba Security focuses on reducing human-driven cyber risks through behavioral insights and targeted awareness strategies. It identifies high-risk users and provides corrective training interventions.
Spade Security utilizes Elba Security to strengthen insider risk management, improve credential protection, and enhance organizational cyber resilience.
Specializations / Specifications:
• Human Risk Assessment
• Behavioral Analytics
• Insider Threat Visibility
• Targeted Micro-Training
• Social Engineering Risk Reduction
More Than a Firewall — A Fully Deployed Cyber Defense System
Deploying a single security tool is only the beginning. Spade Cyber Security delivers fully integrated defense ecosystems — configured for autonomous threat hunting, AI-triggered breach detection, and real-time Security Operations Center (SOC) response.
From initial vulnerability assessments to live incident mitigation, we transform standard network architecture into an intelligent, resilient cyber security asset.
Why Deploy Through Spade Security?
Spade Security is not just a reseller — we are a deployment and integration partner.
Security-first configuration
On-site deployment & testing
VMS & SOC integration
Secure network architecture guidance
Operator training & SOP development
Ongoing service & compliance updates
Operational Use Cases
Perimeter & Campus Patrol
Autonomous or scheduled aerial patrols provide continuous visibility across large campuses, industrial sites, and secured perimeters — reducing reliance on manual guard rounds while increasing real-time awareness.
Alarm Verification & Rapid Response
Deploy drones immediately after a triggered alarm to visually verify incidents in minutes. Reduce false dispatches, improve response accuracy, and provide live situational intelligence to security teams.
Critical Infrastructure Inspection
Safely inspect substations, pipelines, towers, bridges, and restricted facilities without shutting down operations. Capture high-resolution visual and thermal data for proactive maintenance and risk mitigation.
Construction Site Monitoring
Monitor project progress, secure equipment yards, and document site conditions from above. Improve oversight, reduce theft, and maintain clear visual records for reporting and compliance.
Utility & Energy Asset Inspection
Perform routine and emergency inspections of power lines, solar fields, wind turbines, and grid infrastructure with minimal downtime — improving safety while lowering operational risk.
Event & Temporary Site Security
Provide rapid-deployment aerial coverage for large events, festivals, or temporary work sites. Enhance crowd monitoring, perimeter control, and emergency coordination with live aerial visibility.
Still have questions?
While a firewall is a perimeter tool, we deliver a fully integrated defense ecosystem that includes autonomous threat hunting, AI-triggered breach detection, and a real-time Security Operations Center (SOC) response.
Our architecture utilizes a unique transport plane where all connections are outbound-only to a socket rendezvous point, meaning no listening ports are left open on your local machine to be exploited by attackers.
You receive a centralized “Insights” dashboard providing real-time data on active client counts, firewall status, and ISP quality to ensure your infrastructure is always performing optimally.
Yes, our endpoint management system tracks every workstation by group, OS version, and local IP, providing real-time “Agent State” updates and detailed traffic logs for every device on the network.
The system continuously analyzes traffic patterns and throughput; if a deviation occurs—such as a spike in unauthorized data transfer—the AI triggers an immediate alert to our SOC for mitigation.
Our dashboard monitors ISP quality and throughput (Download/Upload rates) 24/7, allowing for automated failover coordination to ensure your security assets remain online.
We use a “Socket Rendezvous” method where the client initiates an encrypted session (SSN/SSH) through a regional rendezvous point, ensuring end-to-end security without direct exposure to the public internet.
We provide comprehensive traffic logs and campaign results that track success and failure rates across different departments (Sales, Tech, Product, etc.), making it easy to identify and remediate internal security gaps.

Menu

